In the vast and ever-evolving landscape of software development, new contenders frequently emerge, promising innovation and efficiency. Yet, few have garnered the industry-wide attention and rapid adoption seen by Rust. More than just another programming language, Rust represents a paradigm shift, engineered from the ground up to address some of the most persistent and critical challenges faced by developers today, particularly in areas where performance and reliability are paramount. This report undertakes an expert engineering assessment, akin to a rigorous road test, to unpack the foundational principles that define Rust and trace its remarkable trajectory to mainstream prominence.
Our deep dive will explore how Rust balances the traditionally conflicting demands of high performance, typical of languages like C and C++, with an unprecedented emphasis on safety and concurrency. We’ll analyze the innovative mechanisms that underpin its robustness, scrutinizing how these features are designed not just for theoretical elegance but for practical, real-world application. This isn’t merely a technical overview; it’s an examination of a meticulously crafted piece of engineering, designed to redefine what’s possible in system-level programming and beyond.
From its conceptual birth as a personal project to its current status as a preferred choice for critical software infrastructure, Rust’s journey is one of relentless refinement and community-driven evolution. This first section will lay the groundwork, dissecting its core philosophical tenets, the revolutionary ownership model, its pivotal historical moments, and the crucial milestones that propelled it from an ambitious research endeavor to a cornerstone of modern software development, garnering significant endorsements along the way.
1. **Core Philosophy: Driving Performance, Safety, Concurrency, and Memory Safety**Rust stands as a testament to the idea that a programming language can achieve uncompromising performance without sacrificing crucial safety guarantees. Its design ethos revolves around a quartet of pillars: speed, type safety, concurrency, and paramount memory safety. This commitment allows developers to write highly efficient code, comparable to what’s achievable in C or C++, while mitigating entire classes of bugs that plague those lower-level languages. The language is a general-purpose tool, but its true power shines in systems programming where fine-grained control and predictable execution are non-negotiable.
A cornerstone of Rust’s philosophy is its ability to enforce memory safety without relying on a conventional garbage collector. This is a crucial distinction, as garbage collection, while simplifying memory management, can introduce unpredictable pauses and overhead, making it unsuitable for real-time systems or applications requiring deterministic performance. Rust’s approach means that memory is managed deterministically, with very low overhead, aligning perfectly with high-performance computing needs. This design decision directly contributes to its suitability for resource-constrained environments like embedded devices, or high-throughput services.
Furthermore, Rust’s emphasis on concurrency safety is a game-changer. It is explicitly designed to prevent data races—a notoriously difficult class of bugs to debug in concurrent programming—at compile time. This proactive prevention saves countless hours of development and testing, ensuring that multi-threaded applications are inherently safer and more reliable. By addressing these fundamental concerns directly within the language’s core design, Rust empowers developers to build complex, high-performance systems with a confidence previously unattainable without extensive manual oversight and rigorous testing.
2. **The “Borrow Checker” and Ownership System: A Revolution in Memory Management**At the heart of Rust’s memory safety guarantees, and arguably its most distinctive feature, is its innovative ownership system, enforced by the “borrow checker.” This system operates under a strict set of rules that are verified at compile time, eliminating the need for a runtime garbage collector while still preventing common memory-related errors such as dangling pointers. Each value in Rust must have a clear owner, and critically, there can only be one owner at a time. When the owner goes out of scope, the value is automatically dropped, executing its destructor and freeing associated resources.
The ownership system elegantly manages resource lifecycle, adhering to the “resource acquisition is initialization” (RAII) convention. This means that resources like file handles, network sockets, or locks are automatically released when the objects that manage them are dropped, preventing leaks and ensuring proper cleanup. This deterministic management, validated at compile time, provides predictable resource usage and minimizes overhead, a significant advantage for system-level programming and performance-critical applications. It’s a robust engineering solution to a problem that has historically vexed developers.
Complementing ownership, Rust introduces the concept of borrowing through references (`&` for immutable and `&mut` for mutable). These references allow temporary access to a value without taking ownership. The borrow checker ensures that at any given time, there can be either one mutable reference OR any number of immutable references, but not both simultaneously. This rigorous enforcement prevents data races and ensures that all references point to valid memory, eliminating null and dangling pointers. It’s a complex but incredibly effective mechanism that underpins Rust’s unparalleled memory safety.

3. **Historical Genesis: Graydon Hoare’s Vision and Mozilla’s Early Involvement**Rust’s story began in 2006 as a personal project by Graydon Hoare, an employee at Mozilla Research. Driven by frustrations, notably with a broken elevator in his apartment building which highlighted issues of reliability and control, Hoare embarked on creating a language that offered better solutions. In these early years, from 2006 to 2009, Rust was developed in Hoare’s free time, largely unpublicized within Mozilla, indicating a deep personal investment in solving fundamental programming challenges.
Hoare’s vision for Rust was not about radical novelty but about synthesizing “good ideas from old languages” to “save the future from itself.” He drew inspiration from a diverse array of established languages like CLU, BETA, Mesa, Erlang, and Limbo, demonstrating a commitment to proven concepts over untested innovation. This pragmatic approach, focusing on robust, well-understood principles, laid a strong foundation for the language’s eventual stability and effectiveness. The initial compiler itself, written in about 38,000 lines of OCaml, showcased the complexity of the undertaking.
By 2009, a small group at Mozilla became interested, and the project gained official sponsorship. Executives like Brendan Eich recognized Rust’s potential for a safe web browser engine, leading to the allocation of engineers, including Patrick Walton, Niko Matsakis, Felix Klock, and Manish Goregaokar, to the project. This institutional backing, coupled with the dedicated “nerd cave” where developers converged, marked a critical turning point, transitioning Rust from a passionate personal endeavor to a formally supported research and development initiative with significant resources.

4. **Evolution and Stabilization: The Journey to Rust 1.0**The period between 2012 and 2015 was a crucible for Rust, characterized by substantial, often radical, changes that refined its core design and prepared it for stability. This era saw significant transformations to the type system, including the removal of early experimental features like the typestate system and, crucially, the garbage collector. The latter’s removal, by 2013, cemented the ownership system as the sole mechanism for memory management, a decision that would become a defining strength.
Throughout these years, the ownership system was progressively consolidated and expanded, becoming the sophisticated mechanism it is today, adept at preventing memory-related bugs at compile time. Simplifications were also made, with the removal of explicit `pure` annotations for functions and specialized syntax for channels and various pointer types, aiming for a more streamlined and coherent language. This iterative process, influenced by developers from C++, scripting languages, and functional programming backgrounds, honed Rust into a pragmatic yet powerful tool.
Graydon Hoare stepped down in 2013, but Rust’s development continued under a federated governance structure, emphasizing community involvement. A “core team” was established, and a Request for Comments (RFC) process was introduced in March 2014, allowing for open, collaborative discussion and decision-making on new language features. Despite initial concerns about adoption due to rapid changes, this period culminated in the highly anticipated release of Rust 1.0 on May 15, 2015, six years after Mozilla’s sponsorship, signifying a commitment to backward compatibility and stability.

5. **Robust Ecosystem and Early Enterprise Adoption**Following the release of Rust 1.0, the language quickly cultivated a robust ecosystem, essential for its widespread practicality and appeal. The development of the Servo browser engine, jointly funded by Mozilla and Samsung, served as a crucial proving ground, with new Rust features rigorously tested and refined through its implementation. This symbiotic relationship meant that Rust’s evolution was deeply informed by real-world application, ensuring its features were not just theoretically sound but practically effective for complex projects. Firefox itself began shipping with Rust code as early as version 45 in 2016, with Servo components later integrating into Firefox 57 as part of the Gecko and Quantum projects.
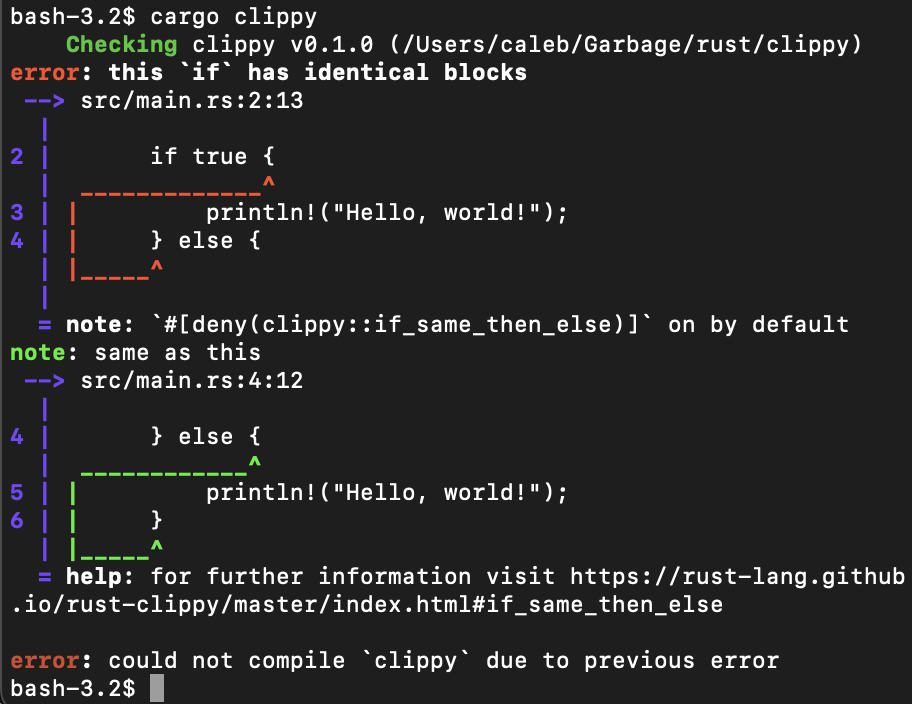
Beyond the browser, Rust’s toolchain ecosystem saw significant improvements. Tools like Rustfmt enhanced code consistency, while better integrated development environment (IDE) support streamlined the developer experience. A regular compiler testing and release cycle further fostered reliability and predictability. This commitment to a comprehensive and user-friendly development environment has been pivotal in attracting developers and facilitating adoption, much like a complete service package enhances the appeal of a high-performance vehicle.
The earliest enterprise adopters, recognizing Rust’s unique benefits, included Samsung, Facebook (now Meta Platforms), Dropbox, and Tilde, Inc., the company behind ember.js, with Amazon Web Services joining by 2020. These pioneering companies acknowledged the inherent risks of adopting a new technology but cited compelling reasons: superior performance, the absence of a garbage collector, inherent safety features, and the overall pleasantness of working with the language. Notably, Amazon developers highlighted research indicating Rust’s energy efficiency, often outperforming Java and C++ in energy consumption, a critical factor for large-scale, environmentally conscious operations.
Read more about: Beyond the Hype: Dissecting the Complex Reasons Why Americans Are Buying Fewer Tablets and What This Means for the Future of Digital Devices

6. **The Rust Foundation and White House Endorsement: Solidifying a Future**The year 2020 presented a significant challenge for Rust, as Mozilla underwent corporate restructuring and layoffs due to the COVID-19 pandemic, leading to concerns about the project’s future. However, this crisis spurred a monumental response: the formation of the Rust Foundation. Announced on February 8, 2021, by a consortium of industry giants—Amazon Web Services, Google, Huawei, Microsoft, and Mozilla—the foundation solidified Rust’s long-term sustainability and independence. This collective backing underscored the language’s critical importance to the tech industry, ensuring its trademarks, domain names, and financial support would be secure, fostering continued development through grants and community support.
The Foundation’s establishment was swiftly followed by influential endorsements that further cemented Rust’s trajectory. In April 2021, Google announced its support for Rust within the Android Open Source Project, positioning it as a robust alternative to C/C++ for system components. This move was a powerful signal of confidence, highlighting Rust’s capabilities for critical, low-level Android development, where memory safety and performance are paramount. It demonstrated a clear shift in industry preference towards more secure and reliable language choices for foundational software.
Most recently, on February 26, 2024, the U.S. White House Office of the National Cyber Director released a 19-page report urging software development to transition away from C and C++ towards memory-safe languages. Rust was explicitly named among these recommended languages, alongside C#, Go, Java, Ruby, and Swift. This high-level governmental endorsement, driven by national cybersecurity imperatives, is a watershed moment, significantly increasing news coverage and validating Rust’s role as a critical tool in building a more secure digital infrastructure. It marks Rust not just as a developer’s choice, but a strategic asset.
Navigating the intricate landscape of a programming language, much like evaluating a high-performance vehicle, requires a deep understanding not only of its foundational engineering but also of its operational mechanics. Having rigorously assessed Rust’s core philosophies and historical trajectory, we now shift our focus to the practical aspects of its implementation. This section will meticulously dissect Rust’s syntax, its robust typing system, advanced memory management, powerful polymorphism, the nuanced concept of ‘Unsafe Rust,’ and the comprehensive toolchain that empowers developers.
Just as a driver needs to understand the controls and feedback systems of a vehicle, a developer must grasp the fundamental syntax and control flow that govern Rust programs. Rust’s syntax, while bearing similarities to C and C++, is meticulously designed to support its safety and performance guarantees. Functions are declared with the `fn` keyword, and output is handled efficiently with macros like `println!`, ensuring clear communication between the program and the user. Each statement in Rust, a deliberate engineering choice, is terminated by a semicolon, contributing to explicit code structure.
Variables, a crucial component of any program, are defined using `let`. By default, these variables are immutable, a design decision that enhances safety by preventing unintentional side effects, much like a factory setting for optimal stability. However, Rust provides the flexibility to declare mutable variables with the `mut` keyword, allowing for controlled modifications when necessary. This balance between default safety and explicit mutability is a hallmark of Rust’s pragmatic design. Furthermore, variable shadowing, where a new variable with the same name can be declared, offers a clean way to transform values without cluttering the namespace, streamlining variable handling.
Control flow in Rust is engineered for clarity and expressiveness, utilizing block expressions delimited by curly brackets. These blocks can evaluate to a value, a powerful feature that allows for concise and functional programming patterns, akin to a modular engine component delivering a specific output. Conditional logic is handled through `if` expressions, complete with `else` and `else if` branches, enabling precise decision-making within the program. Loops, critical for repetitive tasks, come in various forms: `while` for condition-based iteration, `for` for iterating over collections and ranges, and the general `loop` keyword for indefinite repetition until a `break` statement is encountered. This comprehensive suite of control flow mechanisms ensures developers have the precise tools needed for any logical construct.
Pattern matching, facilitated by `match` and `if let` expressions, is another standout feature, offering a powerful and exhaustive way to handle different data states. This allows developers to gracefully deconstruct values and execute specific code paths, enhancing both readability and robustness, much like a sophisticated diagnostic system that precisely identifies and addresses different engine conditions. For example, `match` can elegantly handle optional values, preventing common null pointer errors by explicitly defining behavior for both the `Some` and `None` cases. This explicit approach to handling data variability significantly contributes to Rust’s reputation for reliability.
Read more about: Beyond the Couch: Unpacking Oprah Winfrey’s Billion-Dollar Business Blueprint and Enduring Cultural Impact
8. **The Strong Static Typing System: Primitive and Compound Types**Rust’s commitment to reliability is deeply embedded in its strong, statically typed nature. Much like the exacting specifications that define the components of a precision engine, every variable’s type must be known at compile time. This strictness eliminates entire classes of runtime errors, ensuring that type mismatches are caught early in the development cycle. While explicit type declarations are always possible, Rust’s sophisticated type inference system can often determine variable types automatically, striking a balance between rigorous safety and developer convenience.
At its most fundamental level, Rust provides a comprehensive array of primitive types, each meticulously defined for specific use cases. Integer types, for instance, are named based on their signedness (`i` for signed, `u` for unsigned) and bit width (e.g., `i32` for a 32-bit signed integer, `u8` for an 8-bit unsigned integer), offering fine-grained control over memory usage. Special `isize` and `usize` types dynamically adapt to the target architecture’s memory address bus width, a thoughtful engineering detail for cross-platform compatibility. Defaulting to `i32` for integers and `f64` for floating points further streamlines common usage patterns.
Beyond integers, Rust supports Boolean types (`bool`) for logical operations, representing `true` or `false`. Characters (`char`) are represented as 32-bit Unicode scalar values, accommodating a wide range of global text. Floating-point numbers adhere to the IEEE 754 standard, offering `f32` for single precision and `f64` for double precision, essential for numerical accuracy in scientific or graphical applications. This diverse set of primitives forms the fundamental building blocks upon which all more complex data structures are constructed.
For grouping related data, Rust provides compound types that maintain its strong typing guarantees. Tuples are fixed-size lists that can hold values of different types, offering a lightweight way to combine heterogeneous data, much like a specialized component that integrates different materials. Arrays, in contrast, are fixed-size lists where all values must be of the same type, ideal for homogeneous collections. Both tuples and arrays offer direct indexing for access, providing efficient and predictable data retrieval. This structural integrity, enforced by the type system, ensures data consistency throughout the program’s lifecycle.

9. **Advanced Memory Management: Lifetimes and RAII**While the ownership system establishes who is responsible for a piece of data, Rust’s concept of `lifetimes` and adherence to `RAII` (Resource Acquisition Is Initialization) provides the underlying engine for impeccable memory management. Lifetimes refer to the period during which a reference remains valid, a critical aspect that the Rust compiler meticulously tracks to prevent the notorious problem of dangling pointers. This is not a runtime check but a compile-time guarantee, distinguishing Rust’s approach from languages that rely on garbage collectors.
When a value is “borrowed” using references (`&` for immutable, `&mut` for mutable), Rust’s `borrow checker` comes into play. This sophisticated component of the compiler ensures that references always point to valid memory and that the strict borrowing rules are followed: either one mutable reference or any number of immutable references, but never both simultaneously. This rigorous enforcement eliminates data races and memory corruption at the earliest possible stage, before the code ever runs, much like a pre-flight inspection for a complex aerospace system.
Lifetimes are often inferred by the compiler, but for more complex scenarios, they can be explicitly indicated using named lifetime parameters, typically `’a` or `’b`. These parameters allow developers to specify relationships between the lifetimes of different references in a function signature, ensuring that any returned reference is valid for as long as its inputs. For example, a function that returns a slice of a string might specify that the returned slice has the same lifetime as the original string it was taken from, preventing it from outliving its source. This detailed control over reference validity is a core element of Rust’s memory safety paradigm.
The `Drop` trait further integrates with this system by providing a mechanism for `RAII`. When a value goes out of scope, its destructor (if the `Drop` trait is implemented) is automatically called. This deterministic cleanup ensures that resources—be they memory, file handles, network sockets, or locks—are released promptly and reliably. This approach to resource management eliminates leaks and ensures efficient use of system resources, a critical advantage for system-level programming where every byte and cycle counts. It provides the predictability and control often sought in C++, but with compile-time safety guarantees.
Consider the example of passing a `String` to a function. If the function takes ownership of the `String`, the original variable can no longer be used after the call, as its value has been “moved.” This explicit transfer of ownership prevents double-frees or use-after-free bugs. Conversely, if a function takes a reference (`&String`), it merely “borrows” the value. The original owner retains control, and the value can be used again after the function call, as demonstrated by the ability to call `print_string(&s)` multiple times. This granular control over ownership and borrowing is the bedrock of Rust’s unparalleled memory safety.
10. **Powerful Polymorphism: Traits and Generics**Just as a robust automotive platform can be adapted to produce a variety of vehicle models with shared core functionality, Rust’s `traits` and `generics` provide powerful mechanisms for `polymorphism`, allowing developers to write flexible, reusable code that operates across different types. This bounded parametric polymorphism is a cornerstone of writing expressive and efficient Rust programs. Traits define a set of shared behaviors that types can implement, acting as interfaces that guarantee certain capabilities.
A trait, defined using the `trait` keyword, declares method signatures that any implementing type must provide. For instance, a `Zero` trait might specify a `zero()` method to return a zero-equivalent value for a type and an `is_zero()` method to check if a value is zero. Types like `u32` or `f32` can then `impl` (implement) this `Zero` trait, providing their specific implementations for these methods. This allows developers to define common contracts for behavior, creating a standardized way to interact with diverse types that share a conceptual foundation.
`Generics` enable the creation of functions, structs, and enums that can work with any type, as long as that type satisfies certain `trait bounds`. A generic function, like `zero()`, specifies a type parameter (`Num`) that must implement the `Zero` trait. This ensures that within the function, `Num` will always have the `zero()` method available, regardless of whether `Num` is `u32` or `f32`. This powerful abstraction prevents code duplication and promotes reusability, analogous to designing a universal powertrain that can be fitted to various chassis, optimizing development efficiency.
Rust distinguishes between `static dispatch` and `dynamic dispatch` for polymorphism. Generic functions, by default, use static dispatch, meaning the compiler generates separate, specialized copies of the code for each concrete type used with the generic function (a process called `monomorphization`). This results in highly optimized code that is as performant as hand-written functions for specific types, albeit potentially increasing binary size and compile times. It prioritizes raw performance, much like a bespoke engine tune for a specific racing application.
For scenarios requiring more runtime flexibility, Rust offers `trait objects`, enabling dynamic dispatch. Declared using `dyn Tr` (where `Tr` is a trait), trait objects allow different types that implement a given trait to be treated as functionally equivalent at runtime. Because trait objects are dynamically sized, they must be placed behind a pointer (e.g., `Box`). This enables collections of heterogeneous types that share a common interface, such as a vector of `Box`es holding different types (integers, floats, strings) that can all be `Display`ed. This runtime adaptability provides immense power for building flexible and extensible systems, akin to a modular vehicle architecture that supports interchangeable components.

11. **The Careful Balance of Power and Responsibility: ‘Unsafe Rust’**While Rust is renowned for its compile-time safety guarantees, there are specific, low-level scenarios where these checks need to be temporarily set aside. This is where `Unsafe Rust` comes into play, providing an explicit mechanism to circumvent the compiler’s strict rules. It’s a powerful tool, analogous to disengaging safety features in a high-performance machine for specialized, expert-level operations. However, with this power comes significant responsibility: programmers operating within `unsafe` blocks are solely accountable for upholding Rust’s memory and type safety requirements.
The `unsafe` keyword marks blocks of code where developers are allowed to perform operations that the compiler cannot guarantee as safe. These operations include dereferencing arbitrary raw pointers (`*const` and `*mut`), calling external code through foreign function interfaces (FFI), or performing architecture-specific intrinsics. Other low-level functionalities enabled include volatile memory access, type punning, and inline assembly. Such capabilities are essential for interacting with operating systems, hardware, or libraries written in other languages like C and C++.
Implementing complex data structures, such as doubly linked lists, which often involve intricate pointer manipulation and mutable aliasing, can be difficult or even impossible to achieve purely within Safe Rust’s guarantees. In these cases, `unsafe` blocks provide the necessary escape hatch, allowing experts to manually manage memory and pointers. This is not a weakness of Rust, but a deliberate design choice that empowers developers to tackle the most challenging system-level programming tasks while still defaulting to safety for the vast majority of code.
When using `unsafe`, programmers must meticulously ensure that their code adheres to the fundamental safety invariants that Rust normally enforces. Violating these rules—for instance, creating two mutable references to the same location or accessing dangling pointers—leads to undefined behavior, which can cause unpredictable program crashes or security vulnerabilities. This demands a deep understanding of memory models and careful verification, underscoring that `unsafe` Rust is a realm for seasoned engineers who understand the gravity of its implications.
The interface with C and C++ through `extern “C” fn` for C calling conventions, `#[no_mangle]` for exporting symbols, and `#[repr(C)]` for deterministic memory layouts, is a crucial application of `unsafe` Rust. This enables seamless interoperability with existing codebases, acknowledging that in the real world, systems are rarely built from scratch with a single language. `Macros`, both declarative (`macro_rules!`) and procedural, also extend Rust’s capabilities, allowing for code generation and transformation to reduce repetition, further showcasing the language’s versatility and extensibility beyond its core safety features.

12. **The Comprehensive Toolchain Ecosystem: Cargo and Compiler Backends**No high-performance programming language can truly thrive without a robust and user-friendly ecosystem. Rust understands this implicitly, offering a comprehensive toolchain that streamlines every aspect of software development, from project creation and dependency management to compilation and deployment. This integrated suite of tools ensures that developers can focus on writing code rather than wrestling with build systems, much like a well-appointed garage stocked with specialized tools makes vehicle maintenance a breeze.
At the heart of Rust’s development workflow is `rustup`, the official Rust toolchain installer. `rustup` manages different versions of the Rust compiler (`rustc`), standard library, and associated tools, allowing developers to easily switch between stable, beta, and nightly channels, or target different platforms. This flexibility is invaluable for maintaining compatibility across projects and experimenting with the latest language features, providing a consistent and controllable development environment for diverse engineering needs.
The Rust compiler, `rustc`, is a sophisticated piece of engineering itself. It transforms Rust source code into executable binaries through a multi-stage process: parsing the code into an Abstract Syntax Tree (AST), lowering the AST into an Intermediate Representation (IR), applying optimizations through a compiler backend, and finally, linking object code into an executable. By default, `rustc` leverages `LLVM` as its compiler backend, a powerful and widely adopted technology known for generating highly optimized machine code.
Crucially, Rust is not tied to a single backend; it also supports alternative compiler backends like `GCC` and `Cranelift`. This strategic decision broadens Rust’s platform coverage, allowing it to target more diverse hardware and operating systems, and offers potential improvements in compilation times. The ability to swap out compiler backends highlights Rust’s modular design and commitment to long-term adaptability, much like a versatile vehicle engine that can integrate with different transmission systems.
Perhaps the most impactful component of the Rust ecosystem is `Cargo`, Rust’s official build system and package manager. `Cargo` is the backbone of Rust projects, handling everything from project initialization (`cargo new`), dependency resolution, compilation (`cargo build`), testing (`cargo test`), and running (`cargo run`). It seamlessly integrates with `crates.io`, Rust’s official package registry, where developers can discover, download, and publish `crates` (Rust’s term for packages or libraries). This powerful combination simplifies dependency management and fosters a vibrant, collaborative community, much like a centralized parts catalog and assembly line ensure consistency and efficiency in vehicle manufacturing.
In essence, Rust’s comprehensive toolchain, spearheaded by `rustup`, `rustc`, and `Cargo`, provides an end-to-end solution for modern software development. It embodies the language’s philosophy of empowering developers with both performance and safety, packaged within an environment that prioritizes productivity and ease of use. This holistic approach ensures that Rust is not just a technically superior language, but a practical and enjoyable one to work with, designed to tackle the most demanding challenges of the digital age.
From its revolutionary memory safety mechanisms to its powerful polymorphism and robust ecosystem, Rust emerges as a formidable contender in the programming world. It’s a language meticulously engineered to deliver performance, reliability, and developer confidence, standing ready to power the next generation of critical software infrastructure. Its journey from a visionary personal project to a White House-endorsed solution underscores its profound impact and enduring potential. For developers seeking to build software with the highest standards of quality and efficiency, Rust isn’t just an option—it’s a meticulously crafted machine built for the future.