The motion picture industry, a cornerstone of global entertainment and culture, has long grappled with the insidious threat of piracy. From the days of illicit VHS dubs to the current era of high-definition streaming and torrents, the unauthorized distribution and consumption of copyrighted content remain a significant drain on revenue and a disincentive for investment in new productions. In 2024, estimates placed the annual global revenue loss due to digital video piracy in the tens of billions of dollars, a figure that continues to rise as new technologies emerge and distribution channels proliferate.
The core challenge lies in the speed and scale at which pirated content can be disseminated across the vast digital landscape. A movie released in theaters can be ripped and uploaded to hundreds of illicit sites within hours, reaching millions of potential viewers globally before official distribution channels can even fully roll out. This rapid proliferation makes it incredibly difficult for human teams to identify, track, and remove all instances of pirated content. Furthermore, pirates are constantly innovating, employing techniques such as camcording, screen recording, and even sophisticated digital manipulation to circumvent watermarks and content ID systems, creating a relentless cat-and-mouse game.
However, just as technology fuels piracy, it also offers powerful tools to combat it. Artificial Intelligence (AI), particularly in its advanced forms like machine learning, deep learning, and computer vision, is now poised to revolutionize anti-piracy strategies. AI’s ability to process vast amounts of data at unprecedented speeds, identify complex patterns, and make predictive analyses offers a proactive and scalable solution that was previously unimaginable. This integration is not merely an incremental improvement but a fundamental paradigm shift in how the industry approaches content security, promising a future where creators are better equipped to protect their work and ensure fair compensation.
1. **Digital Rights Management (DRM)**A foundational pillar in the defense against digital piracy, Digital Rights Management (DRM) is a technique specifically engineered to prevent the unauthorized copying and distribution of digital information protected by copyrights. It represents an essential layer of security, embedded directly into the content itself, designed to control access and usage. The objective is clear: to maintain the integrity of intellectual property in an age where digital replication is effortless.
DRM systems primarily function through encryption. By encrypting video content, access is restricted, ensuring that only authorized users with the correct decryption keys can view or interact with the material. This acts as a formidable barrier, preventing illicit users from creating unauthorized copies or disseminating content beyond its intended, licensed scope. It’s an intricate dance between secure delivery and seamless user experience, constantly evolving to stay ahead of illicit circumvention.
While DRM forms a crucial component of any robust anti-piracy strategy, its efficacy is perpetually challenged by the ingenuity of pirates. As technology advances, so too do the methods employed by those seeking to bypass these protective measures. Therefore, content producers and distributors must continuously update and refine their DRM implementations, understanding that this is not a static solution but a dynamic, ongoing process in the fight to secure creative works.
2. **Watermarking**Watermarking stands as another indispensable technological tool in the ongoing battle against video piracy, offering a discreet yet powerful method for content owners to protect their assets. This technique involves embedding an indiscernible digital mark directly into a video stream, serving as a unique identifier for the content owner. The beauty of watermarking lies in its stealth, often invisible to the casual viewer, yet detectable by specialized systems.
The primary function of watermarking is to allow content owners to trace the origin of pirated versions of their work and monitor how it is distributed across various platforms. Should an unauthorized copy surface, the embedded watermark can be analyzed to reveal its source, providing critical forensic evidence. This capability transforms a seemingly anonymous act of piracy into a traceable event, enabling targeted enforcement actions against the perpetrators.
As pirates become more sophisticated in their attempts to remove or degrade these marks, the technology behind watermarking has also advanced significantly. Modern watermarking techniques are designed for robustness, capable of withstanding various forms of digital manipulation, re-encoding, and even partial corruption. This continuous evolution ensures that watermarks remain a potent tool for accountability and deterrence, providing content creators with a vital means to protect their intellectual property.
Read more about: Beyond the Red Carpet Smiles: 12 Oscar Realities That Might Just Surprise You

3. **Content Identification Systems**In the sprawling digital ecosystem of video-sharing services, content identification systems have become an essential automated defense mechanism against the pervasive threat of piracy. These sophisticated systems are specifically designed to automatically detect and subsequently remove unauthorized content, operating at a scale and speed that manual oversight simply cannot match. They act as vigilant digital gatekeepers, protecting copyrighted material across vast online platforms.
The operational prowess of these systems hinges on their ability to examine uploaded videos against an extensive database of copyrighted content. Utilizing sophisticated algorithms, they perform rapid and comprehensive analyses, meticulously comparing newly uploaded files with known intellectual property. Any matches identified trigger an alert, signaling the presence of potentially unauthorized material and initiating the necessary removal protocols. This automated process is critical for immediate action.
These systems are particularly vital for platforms that host user-generated content, where the sheer volume of uploads makes human review impractical. By proactively scanning and identifying infringing material, content identification systems play a crucial role in upholding copyright regulations and safeguarding the legal rights of content producers and distributors. Their continuous improvement is paramount as pirates devise new methods to evade detection.
Read more about: Unpacking the Unsettling Rise in Car Thefts: A Consumer Reports Guide to Understanding and Protecting Your Vehicle
4. **Anti-Piracy Tracking Software**The ubiquitous nature of peer-to-peer (P2P) file-sharing networks presents a significant challenge in the fight against video piracy, demanding specialized tools for effective countermeasures. Anti-piracy tracking software emerges as a critical technological solution in this arena, specifically engineered to monitor these networks and identify individuals or entities engaged in the illegal dissemination of copyrighted information. It provides content owners with intelligence to combat unauthorized sharing.
This software operates by constantly scanning P2P networks, analyzing data traffic, and identifying files that match copyrighted content. It can detect the IP addresses and other identifiers of users who are uploading or downloading pirated material, thereby building a profile of illicit activity. This meticulous tracking allows content owners and their anti-piracy partners to gather evidence, which is essential for subsequent legal actions or issuing takedown notices.
The continuous evolution of P2P technologies and the rise of encrypted or decentralized sharing platforms necessitate equally adaptive anti-piracy tracking software. These systems must be dynamic, capable of navigating complex network architectures and circumventing new obfuscation techniques employed by pirates. Their ability to pinpoint the sources of illegal distribution makes them invaluable in disrupting the piracy ecosystem and protecting intellectual property rights.
5. **Geoblocking**In a globally interconnected digital world, ensuring that content is accessed only within its legally authorized territories is a complex but crucial aspect of anti-piracy strategy. Geoblocking, a technology that restricts access to content based on the user’s geographical location, provides an effective means to achieve this. It serves as a digital border control, enforcing regional licensing agreements and preventing unauthorized cross-border distribution.
The mechanism behind geoblocking typically involves identifying a user’s IP address, which is then mapped to a specific geographic region. If the user’s location falls outside the permitted territories for a particular piece of content, access is denied. This can be used to stop users from accessing illegal content from areas outside of those where it is permitted, thereby upholding the territorial integrity of content distribution rights. It’s a key tool for managing market segmentation.
While primarily used for legitimate content distribution, geoblocking also plays a significant role in preventing piracy by limiting the audience for illicit streams and downloads. By making it harder for pirates to reach viewers in specific regions, content owners can mitigate revenue loss and protect their exclusive distribution partnerships. The precision and adaptability of geoblocking technologies are constantly refined to counter VPNs and other methods used to circumvent geographical restrictions.
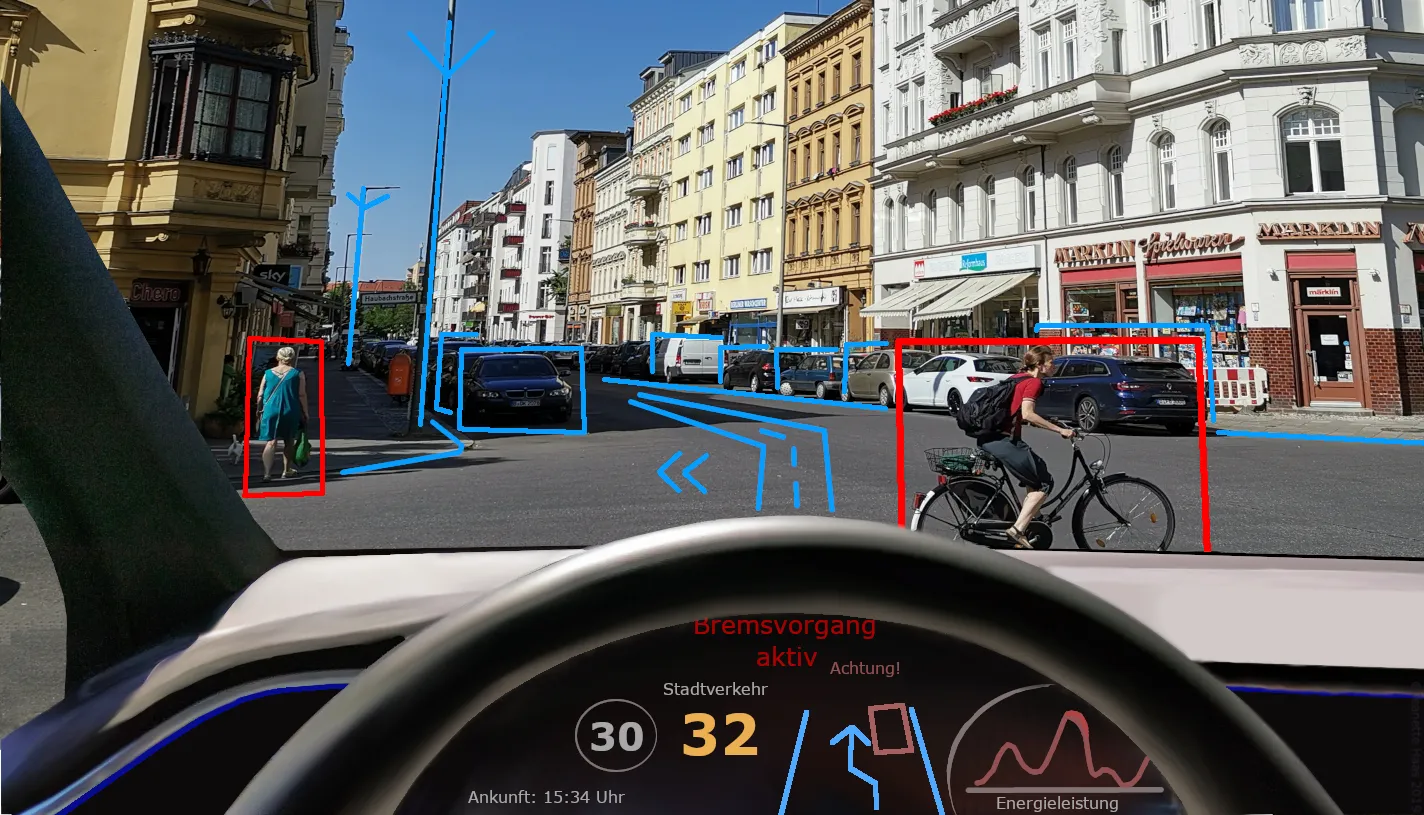
6. **Deep Learning for Anomaly Detection in Video Streams**Moving beyond traditional anti-piracy methods, deep learning, a cutting-edge subset of machine learning, is revolutionizing the identification of pirated video content by focusing on anomaly detection. This advanced AI capability goes far beyond simple file comparisons, leveraging artificial neural networks to discern subtle, often imperceptible, characteristics within video streams that betray unauthorized distribution. It represents a paradigm shift from reactive to highly perceptive proactive defense.
Deep learning models are trained on vast datasets of both legitimate and pirated content, enabling them to “learn” the nuanced visual and auditory signatures of illicit copies. These anomalies might include specific variations in compression artifacts, subtle shifts in color profiles, the tell-tale presence of overlay elements like camcorder time stamps, or unusual aspect ratios. The models become adept at recognizing what a pirated video “looks” and “sounds” like, even after significant manipulation by pirates.
A particularly powerful application is the detection of camcording, which yields some of the first illicit copies after theatrical release. Deep learning models can identify the unique signatures of camcorded content, such as shaky camera movements, distorted audio, or reflections of a cinema audience. By analyzing temporal sequences and spatial patterns, these AI systems pinpoint anomalies with high accuracy, even if the video is cropped or re-encoded, allowing for near real-time identification and swift takedown actions.
7. **Machine Vision for Watermark and Forensic Mark Analysis**While watermarking has long been a foundational strategy, the increasing sophistication of pirates in removing or obscuring these marks necessitates an equally advanced response. Here, AI-powered machine vision steps in, transforming how watermarks are detected, analyzed, and leveraged as forensic evidence. This technology enhances the resilience of watermarking, even against determined attempts at circumvention, by providing unparalleled analytical depth.
Machine vision algorithms are rigorously trained to not only detect the presence of watermarks but also to meticulously analyze their integrity and extract embedded information, even when marks are heavily degraded or partially removed. For instance, a robust machine vision system can identify a perceptual hash embedded within a video. This unique digital fingerprint of the content remains consistent even after minor modifications like re-encoding or resizing, allowing for precise origin tracing.
Beyond overt watermarks, AI-powered machine vision excels at forensic analysis, seeking out minute, often imperceptible, “forensic marks” unique to each legitimate copy distributed. These might include specific pixel variations, subtle noise patterns introduced during encoding, or unique digital signatures embedded at the sub-pixel level. When a pirated copy is discovered, these algorithms can compare these details against a database, tracing the illicit content back to its specific source, thereby pinpointing the leak.
Navigating Future Battlegrounds: Advanced AI Strategies and Collaborative Responses to Emerging Piracy Threats in 2025 and Beyond
As we peer into 2025 and the years beyond, the landscape of content piracy is destined to grow even more complex, demanding an evolution in our defense strategies. Pirates are not static adversaries; they possess a deep understanding of technology and a talent for reinvention. The future of anti-piracy, therefore, rests on advanced AI strategies that can not only keep pace but actively predict and counteract these shifting threats, coupled with robust collaborative responses.

8. **Natural Language Processing (NLP) for Forum and Community Monitoring**Beyond simply identifying visual or audio infringements, the next frontier in anti-piracy involves understanding the human element behind the illicit trade. Natural Language Processing (NLP), a sophisticated branch of AI, is now being deployed to monitor vast swaths of online text, including dark web forums, encrypted chat groups, social media comments, and pirate community hubs. These systems are trained to sift through immense volumes of conversational data, identifying patterns, keywords, and subtle linguistic cues that betray discussions about pirated content, the sharing of illicit links, or even the organization of new piracy operations.
NLP’s capability extends to detecting emerging piracy trends and methods by analyzing how new circumvention techniques are discussed or new content is requested. It can identify key individuals or groups orchestrating large-scale distribution efforts, providing invaluable proactive intelligence that allows content owners to intervene before a threat scales. This form of AI moves beyond reactive content removal to understanding the very ecosystem of piracy, enabling more strategic and targeted interventions. By understanding the language of pirates, we can better anticipate their next move.
The real power of NLP in this context is its ability to extract context and intent from unstructured text data. For instance, it can distinguish between general discussions about movies and explicit instructions on how to access pirated versions. This intelligence is crucial for building a comprehensive threat landscape, helping anti-piracy teams to not only react to existing infringements but to foresee potential vulnerabilities and proactively shut down sources of illicit distribution before they even begin to proliferate across mainstream platforms.
9. **AI-Driven Behavioral Analytics and Predictive Modeling**The fight against piracy is increasingly becoming a battle of foresight, and AI-driven behavioral analytics are at the forefront of this shift. These advanced systems meticulously analyze vast datasets of user access patterns, network traffic, and download behaviors, not just of detected infringements but across legitimate and suspicious activities. By building complex profiles, AI can identify anomalous activities that deviate significantly from typical, legitimate content consumption, such as unusual spikes in downloads from a specific IP address, rapid shifts in viewing locations, or patterns indicative of content scraping rather than casual viewing.
Through machine learning and deep learning, these systems develop predictive models that can flag potential piracy hotbeds or individuals likely to be involved in illicit distribution. They learn to recognize the ‘fingerprints’ of a pirated operation, even when specific content hasn’t yet been identified. This allows content owners to move from a reactive stance – waiting for pirated content to appear – to a proactive one, where potential threats are identified and monitored before they cause widespread damage. It’s about predicting where the next wave of piracy will emerge and having countermeasures ready.
The sophisticated nature of these analytics means that they can adapt and evolve. As pirates refine their methods, the AI models continuously learn from new data, improving their accuracy in identifying novel forms of illicit behavior. This includes detecting the use of VPNs or proxy servers designed to obscure location, or sophisticated bot networks attempting to automate content extraction. This constant learning cycle ensures that the anti-piracy defense remains agile, continuously recalibrating its understanding of pirate tactics to stay ahead of the curve in real-time.

10. **Automated Enforcement and Dynamic Takedown Mechanisms**While identifying pirated content is crucial, the ultimate goal is its swift and permanent removal. The scale of digital piracy, however, often overwhelms manual enforcement efforts. This is where AI truly revolutionizes the takedown process, moving beyond simple content identification to automated, dynamic legal enforcement. AI-driven systems are capable of generating and dispatching automated takedown notices at an unprecedented speed, significantly reducing the time pirated content remains accessible online.
These sophisticated platforms are designed to not only issue notices but also to monitor compliance. They can track whether content has been removed and, if not, escalate the enforcement process through subsequent automated legal steps. Furthermore, they excel at identifying and responding to content re-uploads or the creation of mirror sites almost instantly. If a pirated video is taken down from one platform, AI can rapidly scan for its reappearance elsewhere, enabling a dynamic and persistent defense against persistent infringers.
By streamlining these legal processes, AI dramatically reduces the manual overhead traditionally associated with anti-piracy enforcement. This allows human legal teams to focus on more complex cases, while the automated systems handle the vast majority of routine infringements. This scalable and rapid legal action capability is vital in an era where pirated content can spread globally within hours, ensuring that content owners can enforce their intellectual property rights with the speed and efficiency demanded by the digital age.
11. **Combating Infrastructure Parasites: The CDN Leeching Threat**As 2025 approaches, a particularly insidious threat looms: the rise of “infrastructure parasites” through Content Delivery Network (CDN) leeching. Modern content pirates are increasingly sophisticated, exploiting legitimate infrastructure to steal and redistribute content without bearing any of the associated costs. This tactic involves hijacking existing delivery systems, bypassing content creation and licensing expenses, and instead leveraging the robust and efficient CDNs built for legitimate providers to deliver stolen content to their subscribers at virtually no charge. This approach fundamentally differs from traditional piracy, where illicit actors build their own infrastructure, making detection incredibly challenging.
With fierce competition in the pay TV and streaming media markets, legitimate providers often gravitate towards common, cost-effective technology choices for broad content distribution. Unfortunately, this shared infrastructure can inadvertently expose platforms to vulnerabilities that pirates are quick to exploit, leading to forms of piracy like CDN leeching. By the end of 2025, experts anticipate a notable increase in pirated content distributed through such compromised legitimate infrastructure, creating a complex web of unauthorized access that is difficult to untangle.
The most effective defense against CDN leeching is a proactive and continuous security posture. Content owners must implement real-time security monitoring systems capable of detecting abnormal traffic patterns and usage anomalies. This mandates a shift from periodic security audits to embedding security reviews and audits into every stage of the content development and distribution lifecycle, from initial creation to post-deployment. Such an integrated security approach ensures that platforms remain fortified against these evolving, infrastructure-level threats, safeguarding content against subtle yet pervasive forms of theft.
12. **Addressing the Illegal IPTV Explosion with AI**The exponential growth of IPTV services has introduced a new battleground in the war against piracy, where the distinction between legal and illegal providers is becoming increasingly blurred. Pirates are now leveraging the IPTV ecosystem to restream and rebroadcast content, particularly live sports and global events, with unprecedented speed and scale, rendering traditional manual monitoring systems utterly obsolete. This rapid proliferation of illegal IPTV services is projected to continue its upward trajectory in 2025, offering increasingly sophisticated packages of high-quality streams, aggregated content, and user-friendly interfaces that mimic legitimate services.
To effectively combat this threat, content owners must adopt a multi-faceted approach. A critical first step involves deploying advanced forensic watermarks, which are imperceptibly embedded within content streams, to track the precise source of illegal broadcasts. When these watermarks are combined with comprehensive, AI-powered monitoring systems, content owners and broadcasters gain the ability to rapidly trace pirate streams back to their origin and initiate swift shutdown procedures. This proven methodology is essential for stopping piracy at its source, especially for high-profile live events where every second counts.
Furthermore, content owners must employ automated monitoring systems capable of simultaneously scanning and identifying pirated content across thousands of IPTV services. These systems must possess the intelligence to not only detect unauthorized broadcasts but also to trigger immediate actions to prevent further distribution. The strategic objective is to dismantle the operational backbone of these illegitimate services by coordinating efforts to shut down hosting providers, freeze merchant accounts used for payment processing, and block access to delivery server infrastructure. These sophisticated AI-driven security solutions are becoming indispensable in monitoring, detecting, and disrupting large-scale pirate operations, particularly in the fast-paced world of live content.
13. **Navigating the Social Media Piracy Evolution**Perhaps one of the most complex and rapidly evolving challenges for content owners is the transformation of social media platforms into sophisticated piracy networks. Social media has emerged as a primary hotspot for content piracy, particularly for short-form videos and live streams, leveraging platforms designed for rapid content sharing. While current piracy on social media often involves direct sharing, a more advanced trend is the emergence of “signposting,” where platforms are used to direct users to pirated content hosted elsewhere off-platform, making detection and enforcement even more intricate.
Given the significant growth and continued popularity of short-form content, social media is expected to remain a preferred platform for pirates in 2025. As new platforms emerge and existing ones continually evolve their content-sharing features, pirates will be quick to exploit these advancements. The immense scale and dynamic nature of social media present a formidable challenge for content owners striving to monitor and enforce copyright across such a vast and rapidly changing digital landscape, requiring continuous vigilance and adaptive strategies.
Effective anti-piracy efforts on social media demand swift, collaborative, and AI-driven responses. Content owners must establish real-time monitoring capabilities to detect emerging social platforms and cultivate strong relationships with regional social media providers. Partnering directly with these platforms to integrate with their specific content protection tools is paramount. Additionally, leveraging predictive analytics can help identify potential piracy hotspots before they escalate, allowing for proactive intervention. This blend of technological prowess, strategic partnerships, and foresight is crucial for managing the complex and ever-shifting challenge of social media piracy.
Read more about: Driving the Narrative: The Iconic Vehicles of Stranger Things and Their Unseen Influence
14. **Integrated AI Ecosystems for Comprehensive Anti-Piracy**The future of anti-piracy is not merely about individual advanced AI tools, but their seamless integration into a comprehensive, intelligent ecosystem. Each of the technologies discussed – from deep learning for anomaly detection and machine vision for forensic analysis to NLP for community monitoring and behavioral analytics for predictive insights – gains exponential power when interconnected. This integrated approach allows for real-time data sharing and intelligence across different AI modules, creating a unified defense system that is far more resilient and adaptive than any single solution could be.
Imagine a scenario where a deep learning model identifies a camcorded version of a new release; this information immediately feeds into NLP systems monitoring social media for discussions about that specific pirated title. Simultaneously, behavioral analytics might flag unusual traffic spikes from an IP address linked to the content’s initial leak, while automated enforcement mechanisms prepare takedown notices. This synergy transforms the anti-piracy effort into a truly ‘living’ defense system that learns from every attack, continuously refines its detection capabilities, and optimizes its response strategies in real time.
This holistic, AI-powered ecosystem represents a fundamental shift in the battle against content piracy. It moves beyond a piecemeal approach to establish an intelligent, adaptive shield around intellectual property, ensuring that creators are better equipped to protect their work and foster a sustainable environment for the entertainment industry. The combined strength of these sophisticated AI tools, working in concert, offers the most robust path forward to not only mitigate financial losses but to secure the very future of creative innovation in the digital age.
The challenge of video piracy remains a serious and evolving threat to the entertainment sector, demanding constant vigilance and adaptability. As new technologies emerge and pirate tactics become ever more sophisticated, the strategic integration of advanced AI solutions – from deep learning and machine vision to natural language processing and predictive analytics – is proving indispensable. Coupled with collaborative initiatives and a proactive approach to emerging threats like CDN leeching, illegal IPTV, and social media piracy, the industry can create a powerful, multi-layered defense. By embracing these cutting-edge strategies and fostering a global culture of respect for intellectual property rights, we can collectively steer towards a brighter, more lawful horizon where creative works thrive and are justly compensated, ensuring the entertainment sector continues its vibrant growth into the future.